I’ve confirmed at least one case of Trojan:Win32/Ymacco.AB05 and Program:Win32/Vigram.A from the file “wingit-136.zip” (Index: if-archive/programming/glulx/interpreters/git) Do NOT attempt to download this file, the trojan will actively escape the zip file. This is self replicating, and it took me an hour and a half to purge it from my system. I’ve already tried to notify site staff of the issue in an email but I want to mention this here as well in case other files may be infected.
Eek! Thank you for warning us!
What does “the trojan will actively escape the zip file” mean?
ClamAV doesn’t find anything.
What virus scanner are you using? Virus Total says it’s clean, and it checks it against a ton of databases.
As far as I know, it’s not possible for a virus to escape a zip file unless you run the executable inside it (because it extracts to a temporary folder which is no different than extracting it normally). I was googling to see if that situation has changed, but all I found were sites agreeing with me.
I’m not trying to say you’re wrong, because I do believe you were dealing with a virus problem, but it just leaves me with a lot of questions.
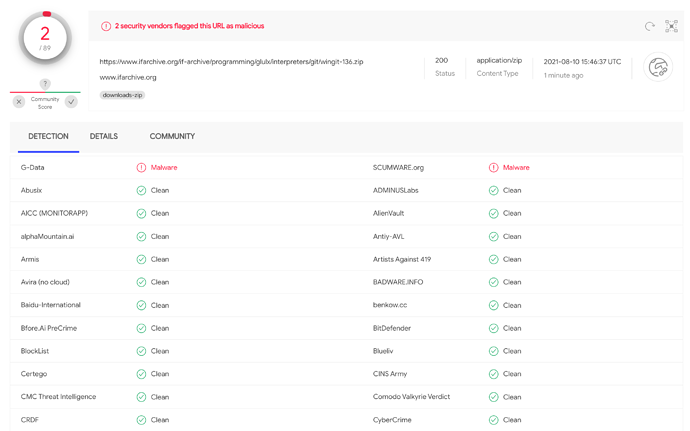
That was a cached result from June. Rerunning the scan does show two hits:
Unfortunately VirusTotal doesn’t seem to show any more specific results…
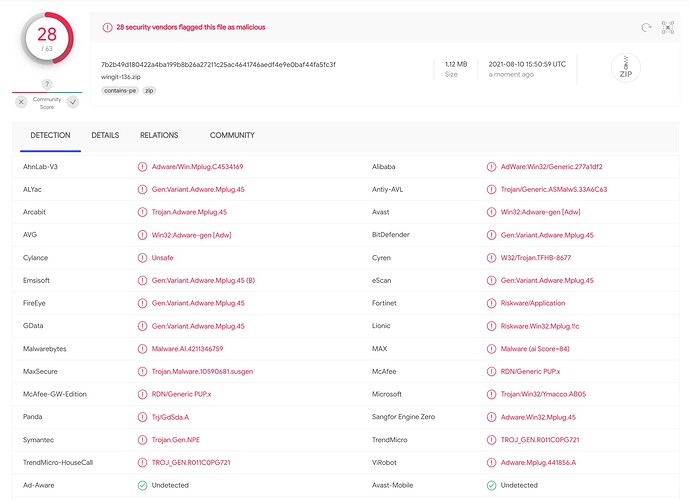
EDIT: Downloading the ZIP file and uploading it to VT paints a rather more sinister picture:
Huh. Stupid site. I don’t know why it wasn’t rechecking when I submitted the link.
But yeah, that looks not great, to put it mildly. One or two could be a false positive, but not that many.
I only navigate with my Android table but thank a lot for the info.
Is this linked with this?
It means the second you download the file it will escape the zip folder. You don’t have to run anything or unzip it to infect you.
Windows defender. I checked it on a virtual machine, it copied itself several times into the Chrome user data cache folder, disguised as a cache file.
If that’s a real thing, then Microsoft is doing very dangerous stuff to their customers. There’s no excuse for treating a ZIP file that way.
It’s amazing and frightening. I use an Android table, is this safe?
This is a false positive from Windows Defender. All anti-virus systems use algorithms to detect patterns in software that indicate infection with a trojan or similar, and every so often they report something that is not really there.
I have double checked this on several systems by rebuilding the allegedly infected executable from source with Visual Studio. It is not infected, but Windows Defender continues to think it is.
The idea that “the trojan will actively escape the zip file” is nonsense.
Well it’s not like they don’t already have a track record of that. The “automatically open attachments” default has got to be one of their most bone headed decisions.
well, the best solution against virii remain Linux…
Best regards from Italy,
dott. Piergiorgio.
A false positive report was submitted to Microsoft, and they seem to have accepted it. Unfortunately the submission page is only visible with my login, but the relevant bit is:
Submission ID: 075f48a6-069c-4d40-ab7d-14997298c41c
Status: In progress
Submitted: Aug 14, 2021 20:10:54
User Opinion: Incorrect detection
Analyst comments:
We have removed the detection. Please follow the steps below to clear cached detection and obtain the latest malware definitions.
- Open command prompt as administrator and change directory to c:\Program Files\Windows Defender
- Run “MpCmdRun.exe -removedefinitions -dynamicsignatures”
- Run “MpCmdRun.exe -SignatureUpdate”